Following on from the previous insight blog series from Turnkey and SAP on Brexit and SAP’s Global Trade Services (GTS) offering, we have collaborated with Paul Lloyd-Smith, Finance and Risk Solution Sales Executive at SAP again. This time we cover cyber-security, cyber-threats and, effective awareness and implementation of practices to reduce the possibility and impact of a cyber-attack.
Why has cyber-security become so significant?
2018 was another record year in terms of the number of attacks experienced by organisations, with 2019 appearing to continue the global trend. Board-level executives now realise that enabling strong cyber-security defences is key to ensuring that the risks they pose to the business are mitigated as much as possible. Failure to keep up to date with the level of malicious activity occurring within a network has been shown to have significant consequences both financially and reputationally, and the impact can be long term once customers and stakeholders realise there is a problem. Re-establishing trust can be a tremendously difficult task. In addition, as the ease of obtaining and storing information increases, the value of data stored by organisations does too. This growth has provided would-be attackers with a greater incentive to infiltrate business critical system(s).
In recent years the threat landscape facing organisations have become more creative, with existing threats evolving over time. ENISA (European Union Agency for Network and Information Security) indicates that the increasingly publicised monetization associated with cyber-crime has attracted more criminal organisations and state-sponsored attacks. Some of the commonest cyber-attacks faced by businesses are explained below:
Social Engineering (Phishing): Email and phishing messages are the primary route into a company’s network. Since people are typically the weakest part of the defences, attackers' focus their attentions on end-users as part of the ‘reconnaissance’ and ‘delivery’ stages of the cyber security kill chain.
Third-Party Targets: As shown in the April 2019 attack at IT consulting firm Wipro, where assumed state-sponsored attackers infiltrated Wipro’s systems and used this to launch further attacks on their client base, trusted third parties can be an attack vector against organisations who themselves have mature defences systems in place.
Internet of Things (IoT): While companies are using a greater number of connected devices to enhance their business operations and productivity, there is an increased risk of would-be attackers gaining access to the network through those with lesser protection mechanisms.
Ransomware: Ransomware such as WannaCry, Petya and NotPetya encrypt the targets files, requiring a ransom before the attackers will decrypt the data. The WannaCry attack on the NHS in 2017 cost an estimated £92m to resolve as a result of lost output and IT costs.
Internal Fraud: The nature of attacks is not limited to the traditional network breaches such as the examples above. Attacks can come from within the business where users have direct access to information systems and can read, download and maintain sensitive data. A common threat example here is that of a disgruntled employee. This type of attack is particularly difficult to defend against since it does not require collusion, and none of the traditional defence mechanisms (i.e. firewalls) provide effective mitigation of these risks.
Is technology keeping pace?
As the threat landscape evolves and attacks become more intelligent, so too do the requirements for monitoring, mitigating and remediating these risks. Cyber-vigilance is a continuous game of cat and mouse as attackers ingenuity outpaces the development of established tools available on the market. While cyber-criminals continuously change their approach in order to surprise organisations and circumvent defences, those on the other side can only provision against known attack methods.
The tools available are only as effective as the content and patterns that are programmed into them. Some of these can be updated using various vulnerability databases, such as CVE, CWE and NVD, but these updates will not be relevant for zero-day attacks which are unlikely to be detected. In the future, it is anticipated that technology on the market will utilise the capabilities of machine learning and AI to identify new threats in real-time, reducing current levels of uncertainty.
The key limitation of most tools on the market is that they work almost exclusively at the network and platform level with binary responses, i.e. your system has either been attacked, or it has not. It does not offer context relating to the information at risk as a result of the access gained to the application layer. Knowing that inappropriate access has been gained to the system is important, but it does not necessarily mean that all data such as customer, vendor, employee or transactional information is now vulnerable. Context is highly important in order to assess the attack's impact, severity and required response.
ERPs are unique in the sense that they utilise far more information and functionality than standalone applications and, consequently, are vulnerable to attack vectors that cannot be detected by traditional tools. For example, if a user has performed debugging activities to maintain code or information directly within tables, the majority of SIEMs would not be able to detect this critical risk. Similarly, once detected, the severity of the impact is greatly dependent upon the specific set of data that has been compromised. It is too simple to suggest that all breaches of an ERP are of the same severity as it will vary greatly on how much of the system has been compromised. For instance, it is more important for an organisation to know whether employee salary data has been inappropriately accessed rather than publicly available information such as store addresses. Likewise, some data within the system is more important from a competitive advantage or security perspective. Where a manufacturer provides standard goods to multiple businesses at a uniform price, the reaction to the loss of shipping data would not be comparable to an instance where the goods are sensitive from a competitive or governmental security perspective, e.g. parts for military equipment or nuclear research.
How can SAP technology assist with cyber-security?
The granularity of security and logging capabilities available with SAP provides a wealth of possibility in terms of being able to log data and provide context to a tool. This allows an almost immediate effective response, without suffering extended lead times as a result of lengthy investigations.
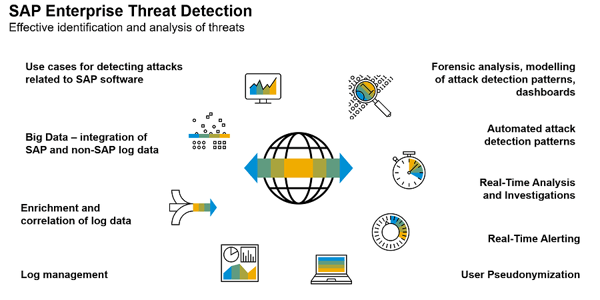
SAP Enterprise Threat Detection (SAP ETD) is a solution that analyses IT security risks in real time in SAP landscapes. The purpose of SAP’s cyber-security solution is to help users neutralise external as well as internal cyber-attacks as they are happening at the application level, especially before serious damage occurs. In contrast to the limitations of the traditional tools noted above, ETD has been built to inherently understand SAP specific risks and report them instantly. To do this, SAP ETD delivers patterns that have been built by SAP Security Experts. The use cases are based on SAP Guidelines such as SAP Security Notes, DSAG Usergroup Guidelines and based on feedback from existing customers.
The solution is not limited to SAP environments, however. The log-learning functionality allows patterns to be executed on information from non-SAP systems. Alternatively, SAP ETD has the potential to feed alerts into other SIEM tools, complementing them by giving the organisation a more holistic view of the network and application layer in one place.
In our next paper, we will be looking at SAP ETD from a more technical perspective to understand exactly how the solution works as well as sharing a date for an invitation-only webinar looking at how the solution works in practice.
If you're interested in learning where your business might be at risk why don't you book a Cyber Vulnerability Assessment with us. To book now just click on the image below.



